Every user of the internet met the term of a firewall. Everyone knows that this is a kind of protection of your network from hackers. But what the firewall really is and how it works? How You can use the Firewall in networking onboard the vessels? Reply to all these questions, You can find in this article!

To explain in a simple way how a firewall works: This is a type of guard that controls the complete traffic. If there is some suspicious movement or data in the network, it protects (is blocking connection or software). Basically, this operation is done by different methods as packet filtering, proxy service, and stateful inspection.
Types of firewall in networking onboard
A firewall can be hardware or software. They work a little bit differently, however, they do a similar job, and they are both qualified as firewalls. They are a wall between your device or your network and the internet. For example, I explain already segmentation here and why it is important. Using the firewall between the segments is also very good practice.
Hardware Firewalls
A hardware firewall is a system/device that works independently from the computer. It protects as a filter of information coming from the outside into the system. Sometimes your router is equipped with broadband, then its have its own firewall. A hardware firewall is connected between the source of a connection and your network. For example, You can connect the OT network to your IT network to send periodical reports.
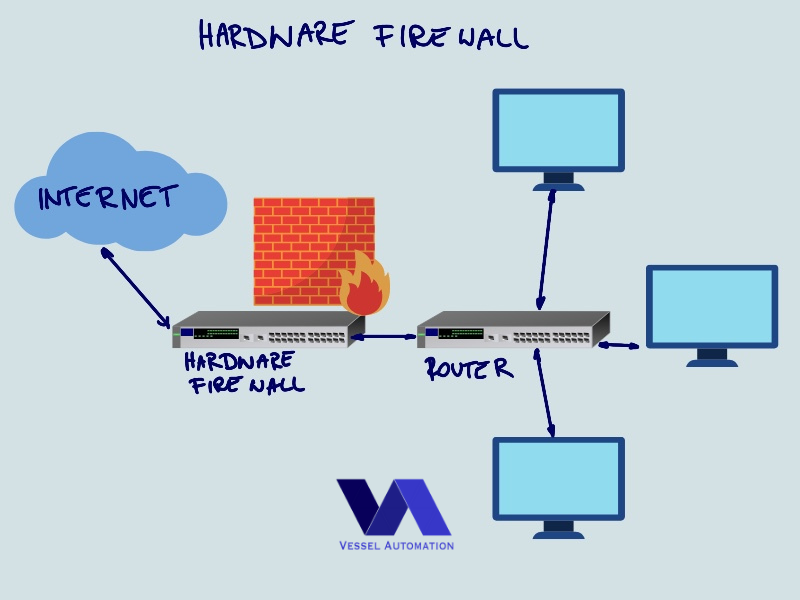
To protect your system, a hardware firewall is checking the data coming from the outside of your computer or your network. All data packages are going through the filter with the “permissions list” to see if it fits correctly with data. That means if You allowed to communicate only on several ports with OT (Operational Technology). This you can arrange by permission list. All other movements, then defined in the permission list in are block. Configuration of hardware firewall requires knowledge and skill.
The biggest advantage of hardware firewalls is the protection of complete networks. Not only a single device. By upgrade/update of one device, you increase the safety of all installations. This is better security than software, because only people who create them, have access to do a reversed engineering.
Software firewalls
The definition of a software firewall is very simple. It is a program installed on the device. Each computer or any other device is inspecting data that are coming in and out of the device. Same as hardware firewalls, the software can be customize to user needs. The software has one big advantage in comparison to the hardware. A big disadvantage of software is, that You have to install it on each device in the network. Similarly with the updates. For each device, You have to do this separately.

The biggest advantage of software firewalls is their size, this is just some MB of your memory. Therefore, they don’t need any additional space and power supply like hardware.
Methods of firewall onboard
Packet filtering
As You know, data is organized in the packages. Therefore, the firewall can be checking complete packages and filter them. If the data package is meeting parameters, then the firewall allows passing. If the data package is different from the parameters, then the package will not go inside the network or device.
Proxy Service
A proxy firewall works as a mirror of your device, placed between your device and network connection. When You try to connect from your device to any website, a proxy service is playing the role of your device. If proxy finds that connection is safe, you establish a real connection to the website. This type of firewall is in use mainly for a web application. However, it is good to have it onboard for crew/recreation networks.
Stateful inspection Firewalls
A stateful inspection firewall keeps a record of a TCP 3-way handshake. Almost all modern networks are equipped with this additional firewall. The stateful firewall is comparing the connection details from client to server in a “state table”. The state table contains details about the source and destination IPs, source & destination ports, TCP sequence numbers, and TCP flags.

The biggest advantage is that this solution is cheap and keeps a record of the entire session. However, this firewall is mainly just an additional safety.
Next-generation Firewall (NGFW)
The next-gen firewall is the most advanced and combined firewall. Basically, they are connecting functions of all other firewalls. They are hardware firewall which provides application-level protection. Compare to a standard firewall, they inspect the entire data transfer with additional features: TCP handshakes, deep packet inspection, surface level, anti-malware functionality. Additionally, they are also the most difficult solution to handle. Therefore, they are the most costly solutions. At the same time, they give the best protection.
Conclusion about firewall in networking onboard
A firewall is the next basic topic, aside from segmentation. I try to describe the main firewall in networking onboard. With a combination of these two solutions, You can increase cybersecurity significantly. The right solution has to be always aligned with the project needs. Different requirements are for merchant vessels than for a yacht or cruise. If You want to look deeper into this topic You can always ask me a question. I can recommend to You also some company that specializes in maritime cybersecurity, which will be suitable to Your company needs.
You reach the end, Well done! If You like this kind of posts, I highly recommend to subscribe our newsletter below!
[…] Therefore, industrial networks need additional hardware. I have described an example of hardware here. With network monitoring devices, movement in the network can be monitored in real-time. However […]
[…] Therefore, industrial networks need additional hardware. I have described an example of hardware here. With network monitoring devices, movement in the network can be monitored in real-time. However […]