Together with Cybersecurity specialists Mission Secure, we have created a new series of articles about Cybersecurity Incidents in the maritime industry. The last thing You want is to find in the headline is that… Your ship is stuck in Panama or Suez Canal because of a Cyberattack. Damages of that attack can reach billions of dollars. Vessels are being more connected than ever before. The risk of a first accident is growing every day. Cyber attacks in the maritime industry are happening, because they are big players with a huge cash flow. They are really good target for a hackers.

Growing numbers of cyber attacks
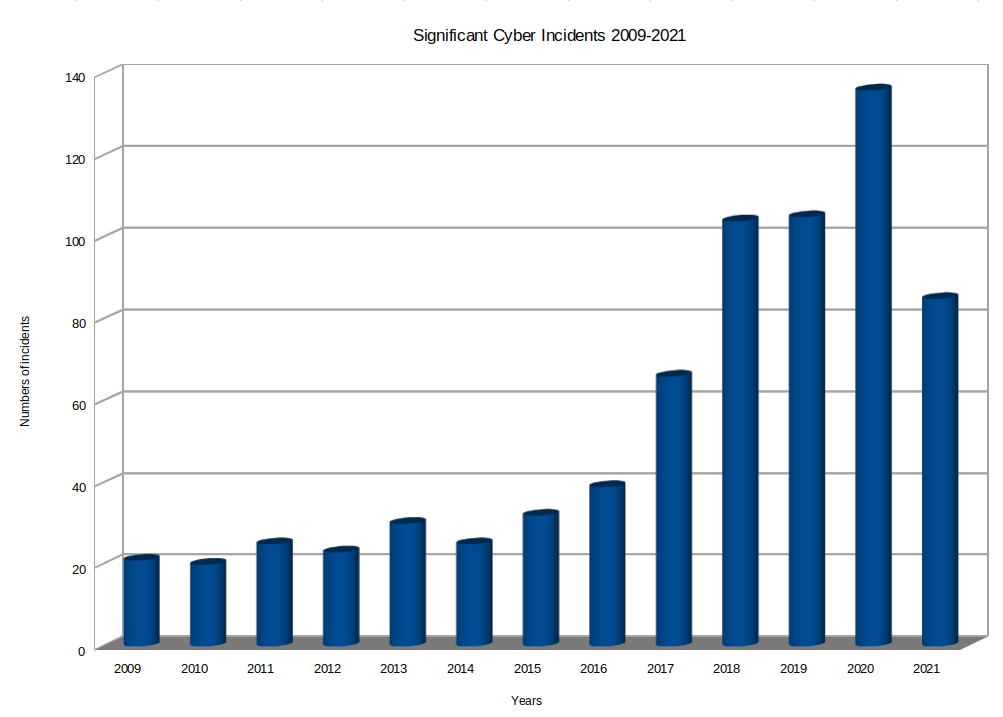
Since the pandemic started, the number of cyber incidents is growing rapidly. Significant Incidents in cybersecurity from all different industries. You can check the website of the Center of Strategic and International Studies here. A full list of accidents recorded from 2006 You can find here. This is clearly showing that the number of incidents is rapidly growing over the years. Especially for You, we have counted all accidents in the last few years. Including all incidents till June 2021. We have counted only significant Cyber Incidents. It means only attack which coast over 1.000.000 US Dollars of cost is significant.
Maritime Cyber Attacks – Maersk June 2017
Danish shipping giant Maersk suffered one of the most high-profile and damaging maritime cybersecurity incidents to date. The largest container ship and supply vessel operator with offices across 130 countries. Over 80,000 employees went dark after being hit with NotPetya.
What’s interesting about NotPetya is that while it has the general characteristics of ransomware, it is not technically ransomware. It’s able to spread on its own without any spam emails or social engineering. It relies on tools like the EternalBlue and EternalRomance exploits developed by the US National Security Agency (NSA). Designed as a wiper, NotPetya encrypts everything in its path. Additionally, it damages the data beyond repair with no way to recover. What was allegedly a state-sponsored Russian cyberattack targeted at Ukrainian companies, NotPetya spread beyond the Ukrainian borders and caused an estimated $10 billion in total damages worldwide.
When NotPetya hit Maersk, it propagated through the network in seven minutes. Computer screens faded to black. Employees scrambled to unplug any connected devices throughout the offices to protect against the fast-spreading malware. Except for an undamaged domain controller from the Ghana office. That had experienced an unrelated power outage, Maersk lost most of its data. Over 49,000 laptops and 4,000 servers were destroyed. In conclusion, the estimation of damages was over $300 million.
Lessons Learned from Maersk
Beyond Protection, Focus on Response Plans. You have to assume that hackers are already in your network. You need extra intelligence to assess what or who is in your network. Maersk has invested in a separate internal threat team. That studies emerging threats and determines how to respond to and mitigate future avenues of attack. Your response plans have to be up to date. These documents and procedures need constant updates! You have to identify any shortcomings and determine new mitigation actions against any emerging cyberattacks.
Establish a Data Protection and Recovery Strategy. Yes, you need to ensure your vessel network and critical control systems are protected. However, You also need a data protection and recovery plan. The best is to have it in place. So that if your network is knocked offline, you can still operate. You also need to rethink your backups. Standard online backups are no longer a safe approach. If your backups are attached to your network, they’re susceptible to attack. Therefore, You need to protect your vessel OT network against data loss. Your company have to be able to reconstruct your database after data loss. Additionally, You should consider offline backups.
Maritime Cyber Attacks – COSCO 2018
Just over a year after the Maersk attack, it was time to find out if the maritime industry had taken steps to strengthen its cybersecurity defenses. That test would come in July 2018, when the China Ocean Shipping Company (COSCO) became a victim of the SamSam ransomware. When SamSam hit, it caused a failure across COSCO’s networks in the United States, Canada, Panama, Argentina, Brazil, Peru, Chile, and Uruguay.
Similar to NotPetya, once SamSam gains access to your network, hackers can gain administrative rights and run executable files without human action or authorization. The group behind SamSam doesn’t push their ransomware as a commodity through a SaaS model – they keep development in-house and update it frequently to avoid enterprise security defenses.
The SamSam attack occurred soon after COSCO acquired one of its rivals, Orient Overseas Container Lines. By activating their contingency plans, COSCO’s operations were back to normal in five days. Any damages from the cyberattack have not been disclosed.
Lessons Learned from COSCO
Segment Your Maritime Networks: Because COSCO had isolated its internal networks across the globe, they were able to contain the damage. Network segmentation helps you reduce the attack surface and is a very useful architectural concept of a defense-indepth cybersecurity strategy. Your OT and IT networks need to be segmented to limit the spread of a cyberattack and stop it from spreading laterally toward your critical vessel controls.
Have a Contingency Plan: As with any organization, those in the maritime industry need to have a contingency plan in place that will keep operations running in the interim while they recover from a cyberattack. In COSCO’s case, they made sure that they had alternative procedures to communicate with customers and deal with service requests. They also utilized social media to reply directly to service requests and updated a FAQ document every time there was a status change. While the process of communicating with customers via emails and phone calls took up a little more time, they were able to continue cargo handling in the United States and Canada without any disruptions.
Maritime Cyber Attacks – CMA CGM 2020
On September 28th, French company CMA CGM reported a cyber-attack on peripheral servers. The company has over 480 ships, operating in 150 different countries. The attack led to limit
ed IT availability across the group, sans CEVA Logistics, due to the company halting external access to applications to prevent the spread of the malware. The company later announced that it also suspects a data breach and is currently assessing the nature and the volume of the affected information.
As of reporting, the CMA CGM eBusiness website and two subsidiaries, Mercosul and Containerships, are again fully operational. The company also announced that maritime and port activities are fully operational. Though the process of restoring full functionality is ongoing, the threat that this attack poses to the shipping industry requires further analysis.
Lessons learned from CMA CGM
Attack has started on the company’s office located in China. Preliminary assessments conclude: the attack is the work of the Ragnar Locker ransomware. This is a kind of encrypting ransomware, first time discovered in December 2019. Ragnar Locker is filtrating and encrypting sensitive data. Payment, release encryption code. The ransomware can be identified with an MD5 hash of 6171000983CF3896D167E0D8AA9B94BA. It serves as the primary indicator of compromise (IoC) for the threat.
The ransomware’s peripheral device discovery feature allows it to spread rapidly to removable and mapped network drives. This explains why CMA CGM’s decision to temporarily disable external features. Notably, the ransomware has a Unicode string comparison function. Ragnar Locker was last seen attacking the EDP energy company in April 2020.
Operational Technology Cyber Attack – Norsk Hydro 2019
A crippling ransomware attack brought Norsk Hydro’s worldwide network down to its knees. Norsk Hydro, fell victim to the LockerGoga ransomware.
LockerGoga’s wrath is especially tumultuous because it disables the computer’s network adapter to disconnect it from the network, changes both user and admin passwords, and logs the machine off. LockerGoga will sometimes leave the victim without the ability to see the ransom message. Or even know that they’ve been hit with the ransomware. Further delaying an organization’s ability to recover their systems.
Norsk Hydro estimated that the hackers had been in their network two or three weeks before they were discovered. With over 22,000 computers and thousands of servers affected over five continents, LockerGoga brought down Norsk Hydro’s entire worldwide network, affecting their production and office operations. The estimation of damages was around $71 million.
Lessons Learned from Norsk Hydro
Be Transparent: Just like Maersk, Norsk Hydro shared more information than usual with the authorities, giving investigators enough information to warn other organizations to prevent similar attacks. Norsk Hydro took its transparency to the next level to keep everyone informed. They held daily press conferences at their Oslo headquarters, set up a temporary website, provided updates on Facebook, and conducted daily webcasts hosted by senior staff who answered audience questions.
Never Let Your Guard Down: It took several months for Norsk Hydro to rebuild its infrastructure. Deploy a new segmentation of the network to ensure that IT and OT are protecting properly. During their initial investigations, they found several variants of the virus that hackers had planted just in case they weren’t successful the first time. Hackers spend many hours developing, testing and executing their attacks, and you need to take that same approach with your cybersecurity strategy. Keeping your networks secure is a company-wide responsibility. It requires consistent security awareness and education for the organization and ongoing monitoring of your cybersecurity framework to minimize risk across your maritime environment.
“Gradually, new computers and servers are connected to these zones. More and more employees can now connect to the network. The danger is still not over.” – Norsk Hydro’s IT Manager
Conclusion about Maritime Cyber Attacks
Norsk Hydro cyberattack isn’t an attack on the maritime industry. But it serves as a wake-up call for the industry. Hackers do not discriminate – they are hitting organizations large and small, with or without abundant cybersecurity resources. Protecting your vessel OT environment is no easy task, but with the right security measures and procedures in place to help you maintain the integrity and continuity of your vessel operations, you’re off to a good start keeping ahead of malicious hackers.
[…] big it is! ( I highly recommend my article about cyberattacks in the maritime industry available here!) There are different ways to be secured in different sectors. Today we will talk about OT […]